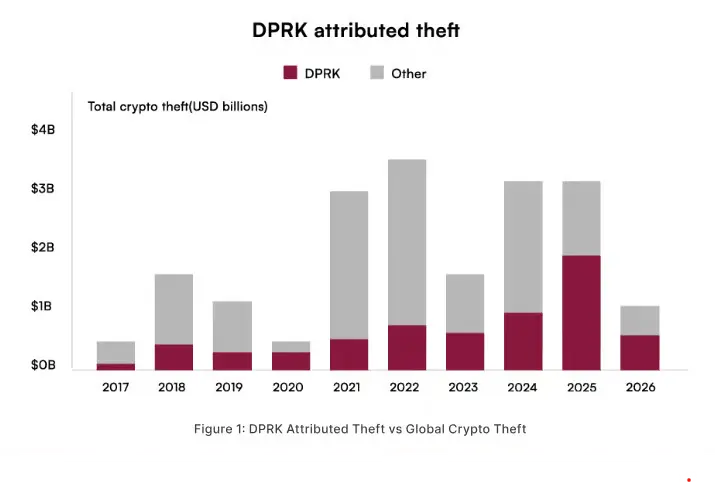
North Korea-linked cybercriminal groups were responsible for the majority of cryptocurrency thefts in 2025, according to a recent report released by blockchain security company CertiK.
The report revealed that hackers connected to the DPRK stole nearly $2.1 billion in digital assets, accounting for around 60% of total crypto-related losses recorded during the year.
Researchers stated that North Korea has become one of the biggest threats to the global crypto industry, especially in the decentralized finance (DeFi) sector.
Since 2016, these groups have reportedly stolen more than $6.7 billion through hundreds of cyberattacks targeting exchanges, protocols, and blockchain platforms.
How DPRK Hackers Are Targeting DeFi Platforms
North Korean hackers are now using more advanced and planned methods to attack DeFi platforms and crypto companies. Instead of random hacking attempts, these groups carefully target employees and systems over a long period of time.
Many attacks start with fake job offers, phishing emails, or fake identities created to trick workers inside crypto projects. Once hackers gain access, they slowly look for weak points in wallets, smart contracts, or blockchain bridges without getting noticed.
Security experts say these attacks are highly organized and supported by state-backed groups. In some cases, hackers spend several months inside a company before stealing funds. This strategy makes it harder for crypto firms to detect suspicious activity early and prevent large-scale financial losses.
Social Engineering Becomes the Biggest Threat in Crypto Hacks
The report identified social engineering as the most effective tactic used by DPRK-linked hackers. Attackers often pretend to be recruiters, investors, developers, or trading firms to gain trust from employees inside DeFi companies.
Source: skynet.certik
One major example highlighted in the report involved the attack on Drift Protocol, where hackers allegedly spent months infiltrating the platform before carrying out a massive exploit worth hundreds of millions of dollars.
Cybersecurity researchers warned that human error continues to be one of the weakest points in crypto security, making social engineering attacks increasingly dangerous.
Billions in Stolen Funds Quickly Laundered
The report also highlighted how quickly hackers move stolen cryptocurrency after an attack. According to researchers, North Korean cybercriminals use decentralized exchanges, crypto mixers, and cross-chain bridges to hide the movement of funds and avoid detection.
These tools help attackers transfer money across multiple blockchains, making it harder for investigators to trace the stolen assets. In one major incident, hackers managed to move and launder more than 86% of the stolen crypto within just one month.
Security experts say these advanced laundering methods are becoming a serious challenge for law enforcement agencies and blockchain tracking firms worldwide.
More: Bitmine Holds 4.3% ETH Supply Earns $319M Yearly
Bybit and Drift Protocol Attacks Raise Alarm
Several major crypto hacks over the past year have raised serious concerns across the industry. One of the biggest attacks targeted Bybit, where hackers reportedly stole more than $1.4 billion worth of cryptocurrency.
Blockchain security experts later revealed that a large portion of the stolen funds was quickly moved through different wallets, decentralized exchanges, and cross-chain bridges to hide the money trail.
Another major incident involved Drift Protocol. In this case, attackers reportedly spent months gaining access to the platform before carrying out the exploit.
Unlike traditional hacking methods, these attackers used social engineering and fake identities to slowly infiltrate the system. Experts say these incidents show how crypto attacks are becoming more advanced and difficult to stop.
Why Experts Call It an Industrial-Scale Operation
Blockchain intelligence firms describe North Korea’s cybercrime operations as highly sophisticated and industrial in scale. Experts say the regime combines cyber expertise, financial networks, and overseas facilitators to support large-scale theft and laundering operations.
Investigators also pointed to underground laundering systems involving OTC brokers, shell networks, and foreign intermediaries that help convert stolen crypto into usable funds.
These operations are believed to play a major role in generating revenue for the North Korean regime amid ongoing international sanctions.
U.S. Authorities Increase Crackdown Efforts
In response to the growing threat, U.S. authorities have increased efforts to disrupt North Korean crypto laundering activities.
The U.S. Department of Justice has reportedly filed multiple asset seizure actions targeting cryptocurrency wallets connected to DPRK-linked operations. Investigators are also working closely with blockchain analytics firms to monitor suspicious wallet activity and cross-chain transactions.
Officials believe stronger international cooperation will be necessary to slow down these highly coordinated cybercrime networks.
Security Firms Recommend Stronger Crypto Security Measures
Cybersecurity experts are advising crypto companies and DeFi platforms to improve their security systems as attacks from North Korean hackers continue to increase. According to security researchers, many hackers gain access through fake job applications, phishing emails, and weak internal systems.
To reduce risks, firms are being encouraged to use stronger identity verification for remote employees, adopt zero-trust security policies, and closely monitor hot wallets and cross-chain bridges.
Experts also recommend regular smart contract audits and employee cybersecurity training to detect suspicious activity early. Security firms believe stronger technical protection and better hiring practices are essential to stop long-term infiltration and future crypto theft attacks.


